Industrial gateways bridge the gap between operational technology (OT) on the factory floor and information technology (IT) infrastructure, translating between diverse industrial protocols while providing edge computing capability and cybersecurity functions. The PCB must support multiple communication interfaces with appropriate isolation while providing processing resources for protocol conversion, data filtering, and local analytics.
This guide covers PCB design considerations for industrial gateways that connect legacy and modern automation systems.
In This Guide
- Multi-Protocol Interface Architecture
- Network Isolation and Security
- Edge Processing Platform
- Power and Environmental Design
- Connectivity and Expansion
- Cybersecurity Implementation
Multi-Protocol Interface Architecture
Industrial gateways connect to diverse equipment using serial protocols (Modbus RTU, PROFIBUS), fieldbus networks (PROFINET, EtherNet/IP), and modern Industrial Ethernet variants. The PCB must accommodate multiple interface types with appropriate signal conditioning and isolation for each.
Serial interfaces remain essential for connecting legacy equipment. RS-232, RS-485, and RS-422 transceivers with industrial surge protection handle connections to PLCs, drives, and sensors that may be decades old. RS-485 networks require proper termination and fail-safe biasing that the PCB must support.
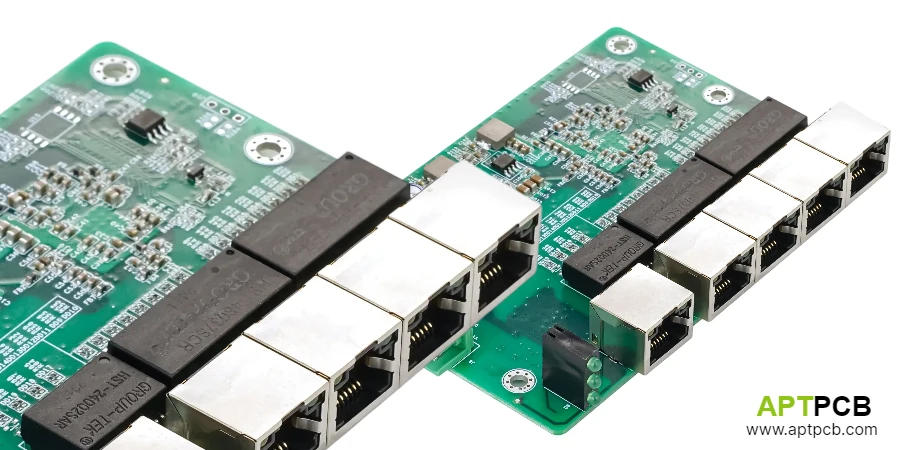
Industrial communication interfaces like PROFINET and EtherNet/IP use standard Ethernet physical layers but require specific protocol stacks and sometimes dedicated hardware for real-time variants. The gateway PCB accommodates multiple Ethernet ports with industrial-grade PHYs and magnetics.
Interface Design Requirements
- Serial Ports: RS-232/485/422 with 15kV ESD and surge protection per IEC 61000-4-5.
- Ethernet Ports: 10/100/1000 Mbps with industrial PHYs; M12 or RJ45 connectors.
- CAN Interface: CAN bus support for CANopen and DeviceNet connectivity.
- Isolation: Galvanic isolation between different network segments; 2.5kV typical working voltage.
- Protocol Hardware: FPGA or dedicated controllers for deterministic protocol handling.
- Expansion Options: Modular architecture for additional interface cards.
Network Isolation and Security
Gateways connecting OT networks to IT infrastructure must provide isolation that prevents network disturbances from propagating between domains. This isolation has both electrical and logical components—galvanic isolation prevents ground loops and transients, while logical isolation through firewalling and protocol validation prevents cyber threats.
Electrical isolation between network ports uses transformer-based Ethernet magnetics or optocoupler/digital isolator solutions for serial interfaces. The isolation rating must exceed the working voltage between networks plus expected transients. PCB layout must maintain creepage and clearance between isolated domains.
Network security functions including stateful firewall, deep packet inspection, and anomaly detection execute on the gateway processor. Processing resources and memory must accommodate security functions alongside protocol conversion without creating latency issues.
Isolation and Security Design
- Port-to-Port Isolation: 2.5-4kV isolation between network ports protects against ground differentials.
- Separate Ground Domains: Each isolated port has independent ground reference; no unintended coupling.
- Firewall Processing: Processor resources budget includes security function overhead.
- Secure Boot: Hardware support for secure boot and firmware authentication.
- Tamper Detection: Optional tamper switches detect enclosure opening.
- Key Storage: Secure element or TPM for cryptographic key storage.
Edge Processing Platform
Modern industrial gateways perform edge computing functions including data aggregation, preprocessing, and local analytics that reduce cloud bandwidth and enable faster response to local events. The processing platform must balance performance with power consumption and cost.
ARM-based processors (Cortex-A53/A72) or x86 embedded processors provide the computing foundation. Selection depends on software ecosystem requirements—Linux-based industrial distributions favor ARM or x86; specific protocol stacks may require particular architectures.
Memory and storage must accommodate operating system, protocol stacks, security software, and data buffering for store-and-forward operation during network outages. The industrial control PCB design must support DDR4 memory interfaces and eMMC or SSD storage with industrial temperature rating.
Edge Processing Architecture
- Processor Selection: ARM Cortex-A series or x86 embedded; balance performance, power, and software ecosystem.
- Memory: 1-8GB DDR4 with industrial temperature rating; ECC option for critical applications.
- Storage: eMMC or industrial SSD; 16-128GB typical; support for data logging and local historian.
- Real-Time Capability: RTOS partition or dedicated real-time processor for deterministic tasks.
- Acceleration: Optional FPGA or AI accelerator for specialized edge processing.
- Watchdog: Hardware watchdog with configurable timeout and recovery actions.

Power and Environmental Design
Industrial gateways operate from 24VDC power common in automation systems, with wide input tolerance (18-32VDC) accommodating the voltage variations present in factory environments. The power system must provide stable supplies to the processing platform while surviving transients and reverse polarity events.
Environmental requirements include -40°C to +70°C operating range for DIN rail mounting in control cabinets, conformal coating for humidity resistance, and vibration tolerance for mobile or harsh installations. Industrial PCB manufacturing must use materials and processes appropriate for these conditions.
Power consumption affects both thermal design and UPS sizing for uninterruptible operation. Efficient power conversion minimizes heat generation in enclosed installations; sleep modes reduce consumption during idle periods while maintaining network presence.
Power and Environmental Design
- Input Range: 18-32VDC with transient tolerance to 36VDC; reverse polarity protection.
- Efficiency: 85%+ conversion efficiency minimizes heat generation.
- Surge Protection: IEC 61000-4-5 surge immunity on power input.
- Temperature Range: -40°C to +70°C operating; -40°C to +85°C storage.
- Conformal Coating: Selective coating for humidity and contamination resistance.
- EMC Compliance: IEC 61000-6-2 immunity; IEC 61000-6-4 emissions for industrial environments.
Connectivity and Expansion
Gateways require connectivity for configuration, monitoring, and optional wireless expansion. USB ports provide local access; optional Wi-Fi or cellular modules enable wireless connectivity for remote sites or mobile applications.
Cellular connectivity (4G LTE/5G) enables remote installations where wired connectivity is impractical. The PCB must accommodate cellular module mounting with appropriate antenna connections and SIM card socket. Cellular module certification adds requirements for SAR and RF testing.
Wireless communication options include Wi-Fi for local connectivity, Bluetooth for configuration, and LPWAN protocols (LoRa, NB-IoT) for sensor network aggregation. Antenna design and placement significantly affect wireless performance.
Connectivity Options
- USB Ports: USB 2.0/3.0 for local configuration, peripherals, or USB-to-serial adapters.
- Wi-Fi: 802.11ac/ax for local wireless connectivity; internal or external antenna options.
- Cellular: 4G LTE Cat M1/NB-IoT or 5G module slot; SIM card socket; antenna connectors.
- Bluetooth: BLE for mobile device configuration and proximity services.
- SD Card: Optional SD card slot for configuration backup or data export.
- Display Interface: Optional HDMI or display connector for local visualization.
Cybersecurity Implementation
Industrial gateways represent critical security control points at the OT/IT boundary. The PCB must support hardware security features that complement software-based protection, enabling defense-in-depth against cyber threats.
Secure boot using hardware root of trust ensures that only authenticated firmware executes. TPM (Trusted Platform Module) or secure element ICs provide tamper-resistant key storage and cryptographic acceleration for secure communications.
Industrial security requirements drive design features including physical tamper detection, secure firmware update mechanisms, and hardware-enforced memory protection that prevents common attack vectors.
Security Hardware Design
- Secure Boot: Hardware root of trust with chain of trust verification through boot process.
- TPM/Secure Element: Hardware key storage and cryptographic acceleration.
- Hardware Crypto: AES acceleration for encrypted communication performance.
- Memory Protection: MPU or MMU enforced isolation between security domains.
- Tamper Detection: Switches detect enclosure opening; optional mesh for physical attack detection.
- Secure Update: Signed firmware updates with rollback protection.
Summary
Industrial gateway PCB design integrates multiple communication interfaces, processing capability, and security features into systems that bridge legacy automation equipment with modern IT infrastructure. The combination of protocol diversity, isolation requirements, edge computing demands, and cybersecurity considerations creates design challenges that require attention to both traditional PCB engineering and emerging Industry 4.0 requirements. Success depends on understanding how these diverse requirements interact and affect system architecture decisions.